Building Trust: Zero Trust Architecture and Mission Partners
Ensuring that the right people have access to the right resources at the right time is a challenge for any organization. This is a simple way of describing the paradigm of Zero Trust. For the modern warfighter, when you add the complexities of the battlefield and partner collaboration requirements, the task begins to feel insurmountable.
Given the Fornetix/GDIT Team’s efforts at Talisman Sabre 2023 (TS23), I’d like to bring attention to several excerpts from the GDIT article and highlight the the value in delivering ICAM solutions to Mission Partner Environments (MPEs):
“MPEs are environments where mission partners can coordinate and collaborate, and ICAM speeds decision making and makes them more secure, thus advancing the vision set forth by the Combined Joint All-Domain Command and Control (CJADC2) initiative.”
Consider the value of simplifying the process of bringing multiple countries together — previously this was accomplished with multiple independent networks. Now with a consistent view of identity through ICAM individuals, technologies, and services from multiple countries can be identified, authenticated, and authorized — allowing for collapsing of networks and more efficient use of communications. All of this enhances command and control and ultimately, lethality.
“ICAM plays an important role in aligning credentials with data, ensuring need-to-know and need-to-access is achieved in a secure manner in an environment where most, if not all, information is Secret or higher in classification.”
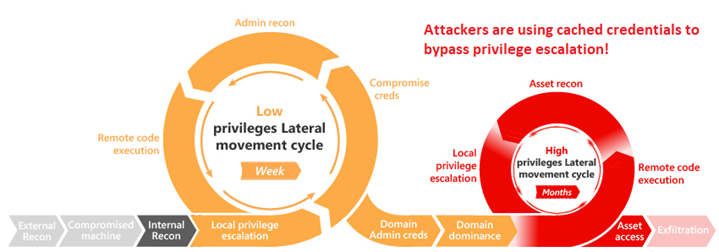
Simply put, having a secure communication (COMSEC) is fantastic. However, it is of far greater importance knowing which users (people, services, and things) are on the network and protecting the data that is being securely transmitted. In practical terms, ICAM helps reduce the number of individual controls that need to be applied because there is consistent source of “truth” through ICAM. The practical implications include single sign-on, transparent authorization, and limited interruptions for multi-factor authentication. These benefits might appear simple, but the impact is extraordinary as properly deployed ICAM allows operators to focus on mission, versus disconnected.
“At the end of the day, MPEs and CJADC2 are close analogs. CJADC2 was created to connect the entire Department of Defense ecosystem and MPE is about ensuring we can connect with mission partners in a secure and seamless way across applications, services. and mission-connected capabilities. ICAM is central to both efforts.”
During TS23, a key part of our approach was enabling data-centric security in the coalition environment. We started working with integration of existing identity providers and tying those together into our ICAM solution.
“Zero Trust and its constant validation of access means we can enable partner access in the same way as internal users. That is to say, when everyone is untrusted, we can treat everyone the same way.”
Our Team has put into practice that ICAM is the foundation of Zero Trust. With that, ABAC is the “lingua franca” between ICAM and Zero Trust controls. Trust becomes something that is fine-grained, additive, and adaptable. Our approach allows us to employ consistent controls for US and our coalition partners so that we have a consistent, modular approach for brining Zero Trust to where mission happens.
“We have a tremendous cadre of global mission partners with different rules governing their data and information assets; but we’re still going to need to communicate with them and share information, securely, at machine speeds. A commitment to ICAM and Zero Trust principles enables that.”
If you have dozens of networks and can’t talk to two of your buddies at the same time – you have a problem. Working with GDIT, our Team and our partners in the Department of Defense are showing a path forward to fewer networks and more time to talk to your buddies. Suffice to say the Fornetix and GDIT Teams’ collective efforts are just the beginning.
To read the full article and gain a deeper understanding of the importance of ICAM and Zero Trust for mission partners, please follow this link: https://www.gdit.com/perspectives/latest/icam-zero-trust-at-the-core-of-interoperability-in-mission-partner/