End-to-End Social Media Encryption Strategies
Would you consider giving up personal data in exchange for a third-party app to show you what your ninety-year-old self will look like? The rise of social media brought lots of joy to consumers’ lives, allowing users to get glimpses of their future selves, to find out their horoscopes, and to communicate with others across the globe. All of this personal data, however, requires companies to take great care in its handling – and recent events have proved that social media doesn’t have a strong grip on consumer privacy. With national crisis like the Edward and the Cambridge Analytica scandal, people are skeptical when it comes to using social media.
Consumers want to know that their data is protected – and social media apps are finally recognizing this demand and implementing End-to-End Encryption (E2EE) strategies that give their users peace of mind. However, this implementation has the potential downside of making it much more difficult to monitor online criminal activity. Read more about what social media encryption strategies are and why it’s becoming more popular.
What is E2EE and Why is it Important?

E2EE is much stronger than other types of standard encryption because no other entity, including the service provider, has the capacity to decrypt the data. E2EE utilizes public key encryption, also known as asymmetric encryption, to store both public and private cryptographic keys solely in the endpoints of the communication. Public key encryption is much stronger than private, or symmetric key encryption, because only half of the decryption key is transmitted over the network. With symmetric encryption, the same key is used at all endpoints, making it much more vulnerable to unwanted third-party access.
Related Blog: The Importance of Encryption in Free Societies
E2EE is important because it keeps your data private and protects it from hackers. Even if the communication server gets compromised, your data is kept secure because no one possesses the decryption keys except you. A strong encryption strategy is especially important in today’s technological climate because of the amount of data breaches that occur on an almost daily basis.
Adopting an E2EE strategy makes personal data secure and builds trust with consumers, which has been proven very difficult to keep. Let’s dive into why E2EE strategies are so vital and why encrypted social media is all the hype right now:
Why Social Media Encryption is a Growing Demand
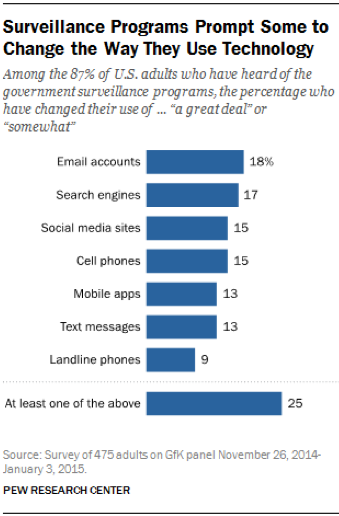
When Edward Snowden leaked information about the government collecting Verizon user data, people responded by changing the way they use technology to communicate. Some even switched their entire channels of communication.
According to the Pew Research Center, out of the 87% of adults who had heard of government surveillance programs, 18% changed their email usage, 15% changed their social media usage, and 13% changed the way they use their mobile apps. These numbers represent a significant shift in public attitude towards social media privacy. The public concern over surveillance and privacy was further increased following the Cambridge Analytica scandal. With millions of Facebook user data exposed, tons of social media sites began to feel the ripple effect and become untrustworthy in the eyes of consumers.
Social media data security has become a factor for users to decide whether or not they use an app. Encrypted social networks are on the rise in response to privacy concerns and the lack of protections.
Social Media Channels with E2EE Strategies
Many social media companies responded to this consumer distrust by implementing E2EE strategies that protects user data against specified threats. Some entrepreneurs detected a business opportunity and created new social platforms altogether. For instance, there’s the launch of ProtonMail, a secure email service with a sophisticated encryption system to deter would-be spies. Or, the creation of Wire by a group of former Skype technologists which relays communications through a network of cloud computers but stores user communications in an encrypted form on the users devices.
The Top 15 Encrypted Social Media Channels:
To get a sense of how prevalent this opportunity is, check out the list below showing just a few out of many social channels that have adopted an E2EE strategy:
|
|
Pros and Cons about Encrypted Social Media Usage
Perhaps the biggest benefit around social media encryption is the peace of mind it gives its users; people feel more comfortable using social channels that have a strong encryption strategy. Knowing that your private data isn’t going to be accessed by third parties is a benefitting factor when deciding which social media channels to use.
From a business perspective, adopting an encryption strategy is just as much a revenue generator as it is a security measure; people want to use what makes them feel secure. Social media giant Snapchat is the most recent popular app to adopt an E2EE strategy. Though it’s too early to tell, the likely outcome for businesses who have adopted an E2EE strategy will be more usage, which ultimately leads to more revenue.
Free Webcast: Controlling Security Vulnerabilities in Automotive IoT
There remains one downside to the heightened social media encryption usage – monitoring criminal activity. Although E2EE is great for blocking hackers’ access to consumer data, it also makes it nearly impossible for law enforcement to pinpoint suspicious online activity or monitor criminal engagement. What’s worse is that the rise of encrypted messaging apps gives terrorist groups more ways to connect. With a plethora of encrypted communication channels for criminals to use, law enforcement will have to rethink their strategy and come up with new ways to monitor online criminal activity.
Where Fornetix Can Help
The same lessons learned with E2EE for social media are applicable to any kind of sensitive data, whether it’s a small mom-and-pop business or a global enterprise. Having a rock-solid encryption strategy in place is a powerful failsafe in the event of a data breach. Even if your perimeter is compromised, any stolen data would appear as gibberish to the attacker. VaultCore by Fornetix breaks down the barriers that have historically inhibited organizations from utilizing encryption to its full potential. Smart automation and scheduling of cryptographic lifecycle tasks keeps your critical data locked down.
If you’re interested in how Fornetix can deploy an effective encryption strategy for your organization, we’d love to schedule a complimentary demo with you.
Note: This entry has been edited to reflect the ‘Key Orchestration’ solution name becoming ‘VaultCore’